The recently disclosed Apache Log4j2 vulnerability (CVE-2021-44228) has serious implications for everything from the cloud to developer tools and security devices. If you are wondering if you are using Log4j in your organization, there is a good chance you are.
You can check the growing list of affected products and services here:
Log4j Vulnerability Being Actively Exploited | New Jersey Cybersecurity & Communications Integration Cell (nj.gov)
If you are following Senturus, you most likely have a BI tool or two as well. The bad news is both Cognos and Tableau use Log4j. The good news is there is a patch you can install today to fix this vulnerability.
What is Log4j?
Log4j is an Apache open-source logging library used by a great deal of companies around the world. This library is used by developers to record how programs run and to assist in auditing and debugging programs.
Why should I be concerned?
The library includes something called “Log4Shell,” which can result in shell access (also called “remote code access”) to a server’s system. This vulnerability allows attackers to download and run scripts on targeted servers, leaving them open to complete remote control. The Common Vulnerability Scoring System (CVSS), which rates software vulnerabilities and scores them with a severity number, rates the Log4j vulnerability as a 10 out of 10.
How concerned should I be?
If you have a Cognos or Tableau server on the public internet, you should highly prioritize patching your system as soon as possible. This vulnerability is being actively exploited today. If you run Cognos or Tableau servers on your internal network, you have some small measure of protection from the private network but should still consider patching these systems a high priority.
Cognos and Log4j
All versions of Cognos Analytics (11.0, 11.1, 11.2) need to be patched. There are interim fixes for the Long-Term Support (LTS) versions of these builds, so if you are not running 11.2 yet, you will need to upgrade to 11.0.13 or 11.1.7 to be able to patch your environment. A patch for non-LTS versions is under development but no date has been released yet. Read full details from IBM.
Tableau and Log4j
All Tableau products (Server, Desktop, Reader, Prep, Bridge) should be patched. The latest version of Desktop, Server, and Reader (2021.4.1) were updated on December 15, 2021 and have closed the vulnerability.
If you are not able to upgrade at this time, scripts can be run along with changes to the system environment variables to close the vulnerability. Read full details from Tableau.
Are Power BI service or Power BI report server affected?
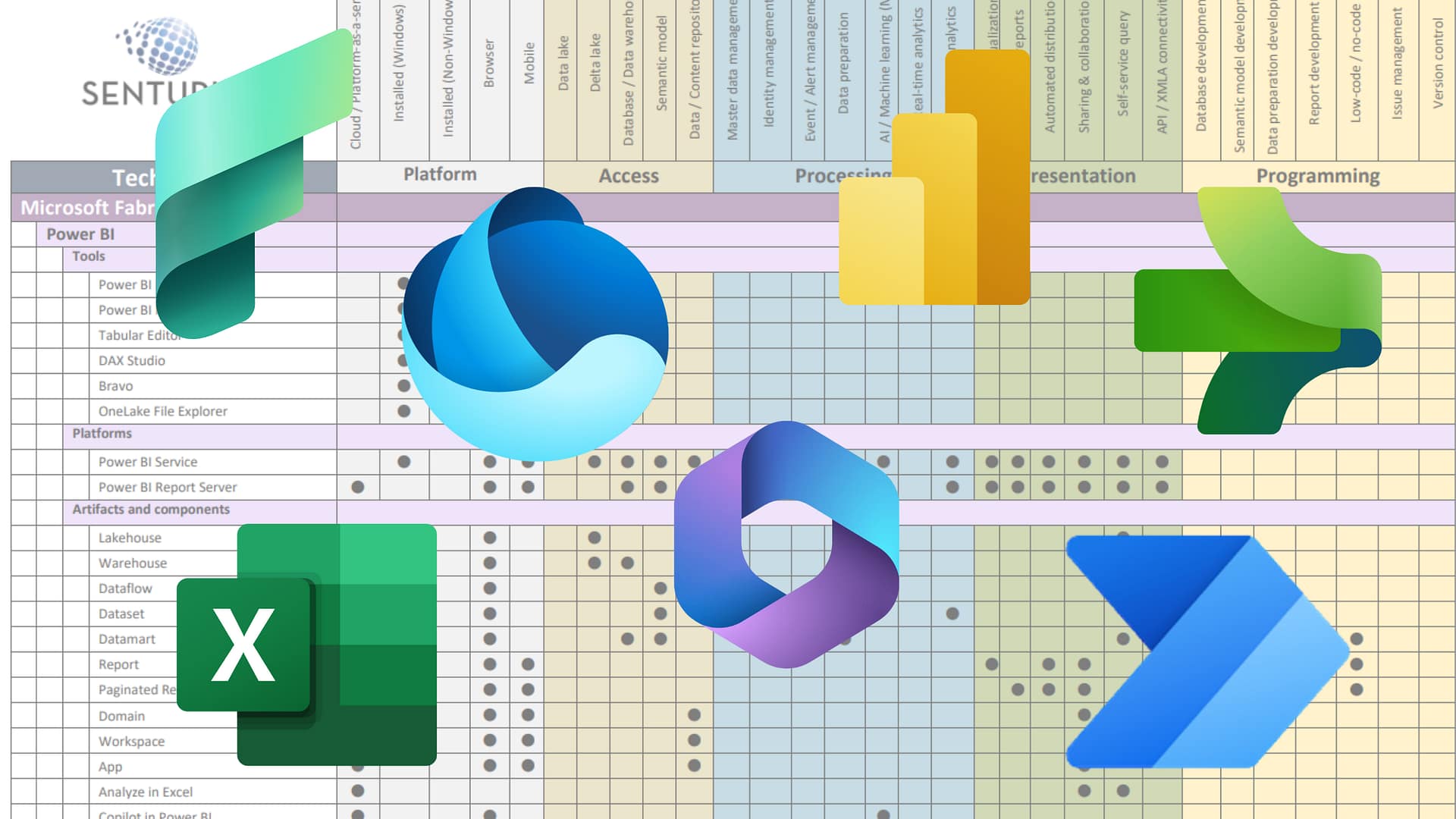
Microsoft has not disclosed any vulnerabilities in the Power BI technology stack for this vulnerability.
“Currently, Microsoft is not aware of any impact, outside of the initial disclosure involving Minecraft: Java Edition, to the security of our enterprise services and has not experienced any degradation in availability of those services as a result of this vulnerability.”
Read the full impact of Log4j in Microsoft’s security response center.
I need help!
Senturus has been working with clients for over 20 years to install, upgrade, tune and secure BI environments to ensure security and smooth performance. Call or contact us today if you need any help with any aspect of your analytics environment. We offer various services including 100% hands-free upgrades. Or, just check in with us to do a simple “sanity check” phone call to make sure you are on the right path.